Source: Komprise
Ransomware attacks are unfortunately becoming so common that it’s no longer a matter of if a company will be attacked but rather when. Gartner predicts that by 2025, 75% of IT organizations will face one or more ransomware attacks.
Two components of Ransomware Protection: Detection and Recovery
Since roughly 80% of data today is unstructured file data, organizations cannot afford to leave file data unprotected from ransomware. Early detection of ransomware can deliver the best outcome, but as ransomware attacks are constantly evolving, detection is not always foolproof and can be hard to do. Organizations should also invest in ways to recover data if they do get attacked by ransomware. An immutable copy of data in a separate location separate from storage and backups provides a way to recover data in the event of a ransomware attack. But keeping multiple copies of data can get prohibitively expensive.
To protect file data from ransomware, the solution must:
- Be cost-effective: An effective solution is to right-size the protection based on whether the data is being actively modified and used or not so that customers don’t have to pay the high cost of multiple copies of all file data.
- Protect if backups and snapshots are infected: Since ransomware can lurk undetected for weeks to months, snapshots and backups might already be infected by the time ransomware fully manifests. Ransomware attackers are also targeting backup software directly, so having your backup software create an isolated ransomware copy may not be effective.
- Provide simple recovery without significant upfront investment: In the event of a ransomware attack, you need to be able to recover your file data—but imagine if you could recover from a ransomware attack without having to pre-provision significant resources, by leveraging environments such as the cloud.
- Be verifiable: As our CEO Kumar Goswami stated in eWeek, the time to validate your plan is before an attack. You must be able to validate that your data is protected and available.
How Komprise Provides Cost-Effective Protection and Recovery of File Data
In a typical organization, 70-80% of file data is cold and has not been accessed in a year or more, yet it continues to consume expensive storage, backup and now ransomware recovery resources. Komprise makes ransomware protection affordable by transparently tiering cold data and archiving it from expensive storage and backups into a resilient object-locked destination such as Amazon S3 IA with Object Lock. By putting the cold data in an object-locked storage and eliminating it from active storage and backups, you can create a logically isolated recovery copy while drastically cutting storage and backup costs.
Create Affordable Cloud Ransomware Recovery Copy that is Logically Air-Gapped:
If you want to use Komprise for both hot and cold data, Komprise can create an affordable logically isolated recovery copy of all data in an object-locked destination such as Amazon S3 IA, so data is protected even if the backups and primary storage are attacked.
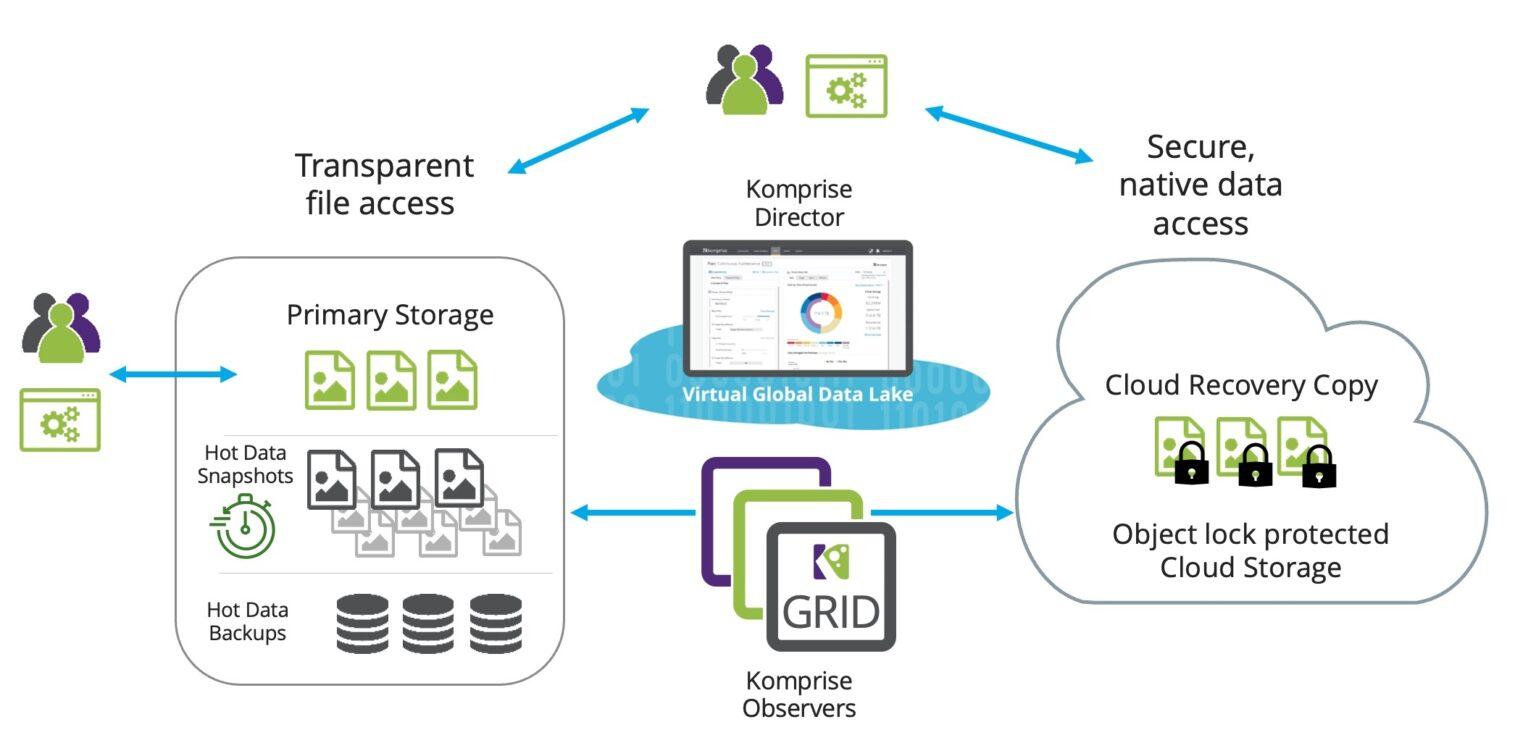
Komprise creates a logically-isolated copy of your file data with the following properties:
- Physical Separation on Immutable Storage: The copy resides on a separate physical location or on a distinct network. For instance, when using Komprise with an Amazon S3 bucket with object lock as the destination, the Amazon S3 bucket is physically separated from your datacenters. This is also an immutable medium to prevent deletion or alteration.
- File-level Isolation: When Komprise moves a file to its destination, the entire file is isolated, as opposed to block-level tiering with backups or snapshots which only isolate parts of the file. This means that if a newer version of a file gets infected with ransomware, you can still recover older versions of the file. Komprise also enables you to detect file modifications on a schedule and copies the modified files as new versions into the Amazon S3 bucket. The schedule can be time-lagged (e.g., once a day or once a week or once a month), to provide greater time separation in the event of an undetected attack.
- Prevent Deletion: You can set the deletion time on the Amazon S3 bucket to a sufficiently long period, such as 12 months, to ensure the copy of the data cannot be deleted even if an attack were to happen on the bucket.
- Instant access and recoverability in the cloud without expensive upfront investments: Komprise copies your files as native objects in Amazon S3 along with all the file metadata intact. You can leverage all the AWS functions and applications on your data directly and view the copied data as files by mounting Komprise. This ensures you do not require expensive backup appliances and other upfront investments to access your copied data.
Ransomware attacks are increasing and the payouts are getting bigger, so doing nothing is not an option.
With backups also coming under ransomware attacks, an isolated recovery copy provides the best protection, but it can get very expensive for the large volume of file data.
Komprise enables organizations to protect file data from ransomware at 80% lower cost through a combination of transparent cloud tiering and replication of all data to an object-locked location with file-level isolation. Komprise cuts active data management costs while enhancing an organization’s ransomware protection posture.
Source: Komprise

